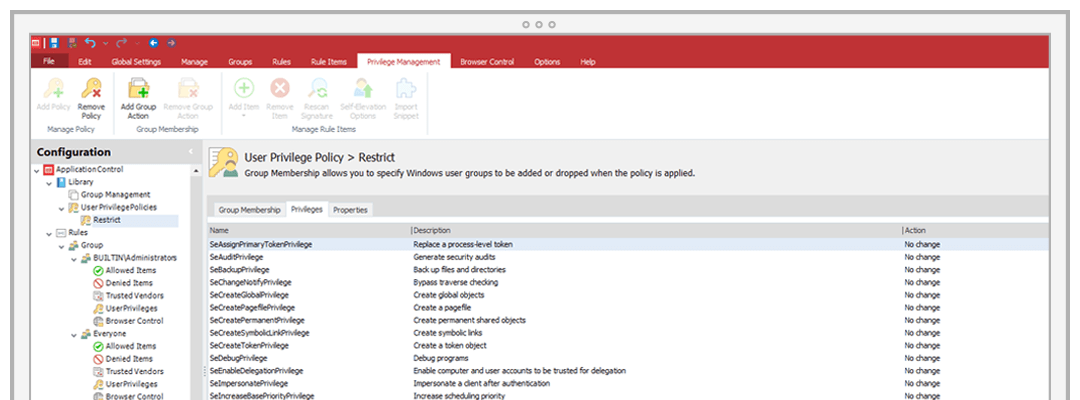
Application Control combines dynamic allowed and denied lists with privilege management to prevent unauthorised code execution without making IT manage extensive lists manually and without constraining users. Automated requests and approvals via helpdesk systems lighten the load for IT staff while providing users a streamlined experience.
Windows
Increase endpoint security and reduce IT workload and cost.